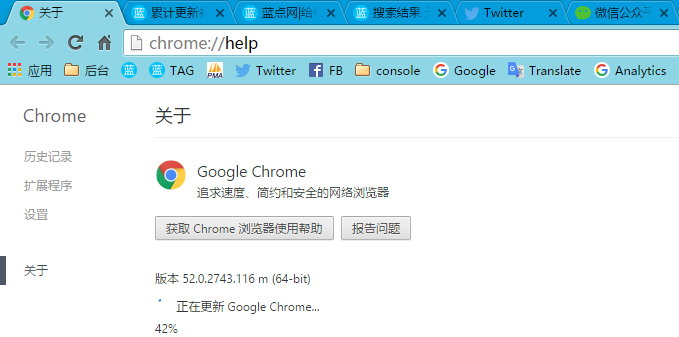
[安全更新]Google Chrome v53.0.2785.89m版发布
Google Chrome 团队今天为 Chrome 用户带来了了 v53.0.2785.89m 版更新,新版本同样是修复了大量已知的 BUG。
近期 Google Chrome 在功能上并没有太多的改进,主要都还是针对安全研究人员上报的 BUG 进行修复。
下载 Google Chrome V53.0.2785.89m 版:
Windows 64 位版:http://xiazai.landiannews.com/files/2016/09/53.0.2785.89_x64.exe
Windows 32 位版:http://xiazai.landiannews.com/files/2016/09/53.0.2785.89_x86.exe
Debian/Ubuntu:http://xiazai.landiannews.com/files/2016/09/53.0.2785.89_amd64.deb
Fedora/openSUSE:http://xiazai.landiannews.com/files/2016/09/53.0.2785.89_x86_64.rpm
MacOS:http://xiazai.landiannews.com/files/2016/09/53.0.2785.89_MacOS.dmg
注意事项:
1、若直接使用浏览器下载过慢请复制链接使用迅雷、旋风、IDM 等下载软件中进行下载;
2、若已安装 Google Chrome 下载离线安装包后双击打开约十几秒后即可更新完成;
3、安装后若想确认是否更新成功可以在本文评论中任意留言即可看到版本号;
以下是本次修复的漏洞列表:
1、安全等级:高 漏洞编号:CVE-2016-5147:Universal XSS in Blink. Credit to Anonymous;
2、安全等级:高,漏洞编号:CVE-2016-5148:Universal XSS in Blink. Credit to Anonymous;
3、安全等级:高,漏洞编号:CVE-2016-5149:Script injection in extensions. Credit to Max Justicz;
4、安全等级:高,漏洞编号:CVE-2016-5150:Use after free in Blink. Credit to Anonymous;
5、安全等级:高,漏洞编号:CVE-2016-5151:Use after free in PDFium. Credit to Anonymous;
6、安全等级:高,漏洞编号:CVE-2016-5152:Heap overflow in PDFium. Credit to GiWan Go;
7、安全等级:高,漏洞编号:CVE-2016-5153:Use after destruction in Blink. Credit to Kettunen;
8、安全等级:高,漏洞编号:CVE-2016-5154:Heap overflow in PDFium. Credit to Anonymous;
9、安全等级:高,漏洞编号:CVE-2016-5155:Address bar spoofing. Credit to Anonymous;
10、安全等级:高,漏洞编号:CVE-2016-5156:Use after free in event bindings. Credit to jinmo123;
11、安全等级:高,漏洞编号:CVE-2016-5157:Heap overflow in PDFium. Credit to Anonymous;
12、安全等级:高,漏洞编号:CVE-2016-5158:Heap overflow in PDFium. Credit to GiWan Go;
13、安全等级:高,漏洞编号:CVE-2016-5159:Heap overflow in PDFium. Credit to GiWan Go;
14、安全等级:中,漏洞编号:CVE-2016-5161:Type confusion in Blink. Credit Trend Micro;
15、安全等级:中,漏洞编号:CVE-2016-5162:Extensions web accessible resources bypass;
16、安全等级:中,漏洞编号:CVE-2016-5163:Address bar spoofing. Credit to Rafay Baloch;
17、安全等级:中,漏洞编号:CVE-2016-5164:Universal XSS using DevTools. Anonymous;
18、安全等级:中,漏洞编号:CVE-2016-5165:Script injection in DevTools. Credit to Panakkal;
19、安全等级:中,漏洞编号:CVE-2016-5166:SMB Relay Attack via Save Page As. Credit to Panakkal;
20、安全等级:低,漏洞编号:CVE-2016-5160:Extensions web accessible resources bypass. l33terally;
有关上述漏洞的详细内容,有兴趣的用户请访问 Chromium Security Page进行了解。